Security and accessibility for services and applications remain top concerns in a world that’s constantly shifting technology-wise, which makes single sign-on (SSO) login an essential asset to ensure users sign in across platforms with ease. In this comprehensive guide, we explore SSO by delving deep into its basics as well as implementation methods and practical examples – exploring its fundamental workings as well as potential benefits.
1. Introduction 1. Introduction & Establishing The Basis Of Business 1. Introduction and Support Services (ITSS)
Single Sign-On (SSO)
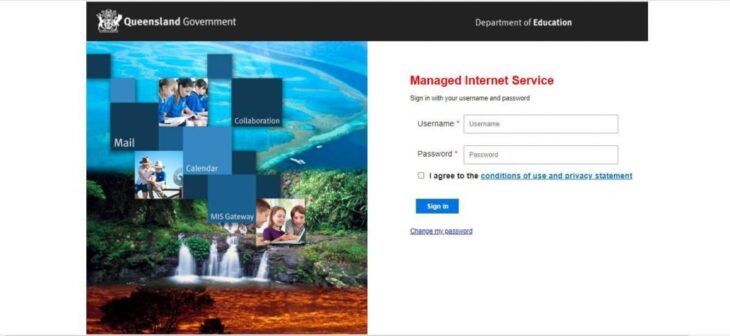
Single Sign-On (SSO) is an authentication system that enables users to sign on once, with one set of login credentials, for multiple applications or services without reentering username/password information each time they gain access. SSO streamlines the authentication process by eliminating repeated entry of username or password information for various systems that share them together – saving both time and effort during authentication processes.
SSO Single Sign On (SSO) has become essential due to the increasing complexity of digital environments. People, whether professional or personal in nature, frequently navigate multiple online platforms simultaneously with individual login credentials for each one; managing all these passwords and usernames becomes cumbersome and may increase risk due to obsolete or weak passwords.
SSO provides solutions by simplifying authentication while increasing both user experience and security. SSO plays an integral part of today’s approaches to access management and identity administration that enable organizations to give their users secure yet seamless access to resources.
2. How SSO Works (For More Details Click here for an explanation)
Before diving deep into SSO it is critical to distinguish between authentication and authorization. Authentication involves validating user identities to confirm they match who they claim they are while authorization involves determining which actions or resources users can access after being authenticated.
SSO systems focus mainly on authentication, making sure users log into one account to gain access to various apps and other services. Authorization decisions typically are handled separately either within individual applications themselves or through centrally managed authorization systems.
SSO Components
SSO relies upon several key components for its operation:
Identity Provider (IdP): The Identity Provider is the primary authority responsible for authenticating users. They verify identity before issuing either an electronic token or a statement confirming the successful authentication of each individual user.
Service Provider (SP): An SP is any service or application users want to access and rely on IdP in order to authenticate users and make decisions based on information supplied from IdP.
User To begin their authentication, end-users begin the authentication process by trying to gain entry to an SSO-protected website and providing their account login password and IdP credentials for validation.
SSO Protocols: SSO utilizes various protocols such as SAML (Security Assertion Markup Language), OAuth, and OpenID Connect in order to transfer authorization and authentication data between an IdP SP and SPs.
Also Read: Hydraulic Systems: Powering Industries and Machinery
An SSO process typically includes these steps.
Users Access Request Users Access Request: A user attempts to gain entry to an SP-protected resource or application.
Redirecting to IdP Once the SP detects that an individual has not registered with us, they are taken directly to an account login page for IDPs.
User Authentication A user provides their credentials (usually email address and username) for verification by an IdP, who then validates them before accepting or declining them for use on its system.
Generating Token After successful authentication, an IdP generates an assertion or security token with details regarding both user identity and authenticity status.
Response Token An IdP transmits its token at SP.
Access Granted HTML0: The SP verifies that the token has been issued legitimately before checking if a user can gain entry to a resource requested.
User Access Granted If the token’s validity has been validated and it has been granted permission by its administrator for access, then SP grants access without further authentication being necessary.
This process occurs quickly and effortlessly for users while assuring security.
3. Benefits of Service Support Organization (SSO).
One of the primary advantages of SSO is an enhanced user experience. Users no longer need to keep track of multiple usernames and passwords for various applications – making login easier, decreasing frustration levels and ultimately improving overall satisfaction levels for the end-users.
Contrary to popular opinion, SSO can actually improve security. By enabling companies to implement rigorous authentication techniques at an IdP level – such as multi-factor authentication (MFA). Users tend to accept and implement strong security measures more readily when only needing to authenticate once.
SSO allows for centralized control of user access and rights. As soon as a user leaves or changes roles within an organisation, their access is instantly cancelled out from all connected applications to reduce unauthorised entry and prevent accidental uninstallation of applications or access.
Reduce Password Fatigue managing multiple passwords and usernames could result in “password fatigue,” where users use weak, easily guessable passwords on multiple websites; SSO provides a solution as users only need one account at any given time.
Centralized User Management from SSO provides organizations with central management of users. Provisioning, deprovisioning and access control processes are managed more effectively from one central point – thus decreasing administrative workload as well as errors due to miscommunication or oversights.
4. Methods for Implementing SSO SSO can be implemented using various techniques and technologies tailored specifically to an organization’s requirements and needs, providing numerous ways for it to be put in place:
Federation-Based SSO
Federation-based Single Sign On is one of the more prevalent SSO implementations, often used for authentication between an identity provider (IDP) and multiple service providers (SPs) who trust each other enough to share authorization and authentication data seamlessly – for instance using SAML (Security Assertion Markup Language) or OAuth protocols as trusted relationships (federations relationships) are formed among IdP and SPs for this to take effect.
Web SSO and Enterprise SSO
Web SSO was specifically created for use with internet-connected software and applications, such as email clients. This type of security allows users to securely access various organizations’ web-based services – for instance logging in via Google for email accounts and third-party providers like Facebook logins for third party services.
Enterprise Single Sign On, on the other hand, is specifically tailored for use within organizations and makes accessing enterprise resources and applications much simpler, improving efficiency and security in doing so. Solutions like Microsoft Azure Active Directory or Okta provide enterprise SSO services.
Also Read: Boost Your Instagram Experience with the Instagram Download Reels App: Unleash the Power
Social Media SSO
Many mobile and online applications now provide Social Media Single Sign On (SSO), which enables users to sign into accounts like Facebook, Google+ and Twitter directly within an application – thus simplifying registration and login processes both for the users as well as app developers.
5. Real-World Implementations Examples for SSOWant to see some real world examples of Single Sign On? Here are a few:
Google Single Sign-On
Users often rely on the Single-Sign-On (SSO) feature of the web for authentication to a variety of services like Gmail, Drive and YouTube without needing to reenter credentials each time they need access. OAuth-based authentication for third-party apps makes Google an attractive solution for developers as well.
Microsoft Azure Active Directory is an access and identity management solution with single sign-on (SSO). Azure AD allows organizations to manage user identities and gain access to Microsoft 365 apps, Azure services, and various applications – in particular via SSO protocols like SAML or OpenID Connect.
Numerous mobile and online websites now provide the ”Login with Facebook” SSO option as part of registration processes, enabling users to log-in directly using their Facebook credentials for easy and hassle-free registration. Furthermore, Facebook Login grants developers access to user data (with user consent), making creating profiles easier while personalizing user experiences even further.
6. Challenges and Considerations
While SSO presents many advantages, there may also be drawbacks and factors to take into account:
Security Concerns
One Point for Falter: Should an IDP experience downtime or an incident that compromises its security, access could become unavailable to all services connected.
User Consent: SSO implementations often require users to sign a consent form so their personal data can be shared among services, so organizations must manage user consent in a secure way and protect data privacy in accordance with legal guidelines.
Phishing Risks in SSO: SSO systems may be vulnerable to phishing attacks, where malicious actors mislead users into providing their passwords and personal data to fraudsters.
Respecting established SSO standards is vital to ensuring compatibility and security when it comes to SSO implementations, with SAML, OAuth, and OpenID Connect being some examples of such foundational requirements for security-conscious SSO implementations.
SSO in a BYOD World
With BYOD policies becoming more prevalent, companies must adapt and secure SSO solutions so as not to cause disruption across various platforms and devices.
Future Trends in SSO
With technology continuously progressing, SSO stands to expand and adapt in various ways:
Utilizing passwordless SSO; biometric authentication techniques or hardware tokens will reduce reliance on traditional passwords while increasing security.
Multi-Factor Authentication (MFA) MFA will become an essential feature of Single Sign On (SSO), to further increase security.
Zero Trust Security
A Zero Trust security model – where no device or user identity is automatically protected from attack by default - has serious ramifications for Single Sign On implementations, necessitating continual user identification verification as well as device protection measures. This requires consistent verification for SSO implementation.
Conclusion
Single Sign-On (SSO) Login has revolutionized how individuals and businesses manage access to online resources. SSO makes authentication faster, secures systems better, and improves customer experiences more swiftly – an indispensable aspect of modern identity and access management strategies.
SSO remains an invaluable tool for companies, enabling safe access to apps and services while adhering to changing trends and taking measures to address security concerns. By harnessing its full power for improved efficiency and user convenience in today’s digital landscape.















You must be logged in to post a comment.